You wouldn’t leave your office door unlocked, so why would you let your website be a free-for-all?
Advancements in technology have critically changed the way businesses need to think about website security. In the third quarter of 2017, Australia actually received the third most amount of web application attacks in the world – a total of 19 million breaches throughout the duration.
From the huge amounts of data available to hackers, through to ransom scams and complete crashes – knowing how to keep safe and secure in the age of digital takes due diligence.
But it doesn’t have to be all doom and gloom – there’s plenty of avenues to take in order to keep safe from hackers and external threats. It just means keeping up-to-date with what’s going on in the online space.
Types of vulnerabilities
Delving into the variations of attacks that take place these days can be a little overwhelming, so it’s worth taking a step back and understanding why hackers even do it in the first place. In a nutshell, it’s like any other breach: they’re able to get something advantageous out of it, and in this case, it’s usually critical data from your business or its visitors.
We’ll give you a quick note to beware the jargon, but some of the most common attacks to watch out for include:
SQL injection: where a hacker utilises specific application codes to get into your database content (SQL), and disrupt or corrupt it. When successful, the hacker is able to manipulate, create or completely delete data in your storage.
Cross site-scripting: also known as XSS, cross-site scripting means the attacker injects specific code into your own script (particularly JavaScript) to then make the script act they way they want. This usually gives them the ability to hijack user sessions and view private information, vandalise the website itself or redirect to unsecure and malicious external websites.
Session management and broken authentication: essentially, this method lets the attacker assume the identity of a user by hijacking their active session, if all the authentication aspects on your website aren’t protected.
Remember, these are only a few of the many types of vulnerabilities floating around on the web. And as these attacks evolve and continue to adapt to security measures, understanding how to keep up with protective efforts becomes even more critical.
Quick steps to keeping your website safe
There’s no one fast way of keeping your site out of the hands of attacks, but there are many little preventative measures you can take. While having an expert on hand is always the best route to opt for, other precautions include:
Watch your coding: remember that sneaky SQL buzzword we mentioned earlier? Although this one’s a little more complex than other steps, it’s still worth noting. SQL is a type of code that you want to keep an eye on. If bits and pieces have been added, there’s likely someone on the other end of it...and not anyone good either. It’s best to get someone who knows how to assess your coding to check for any irregularities.
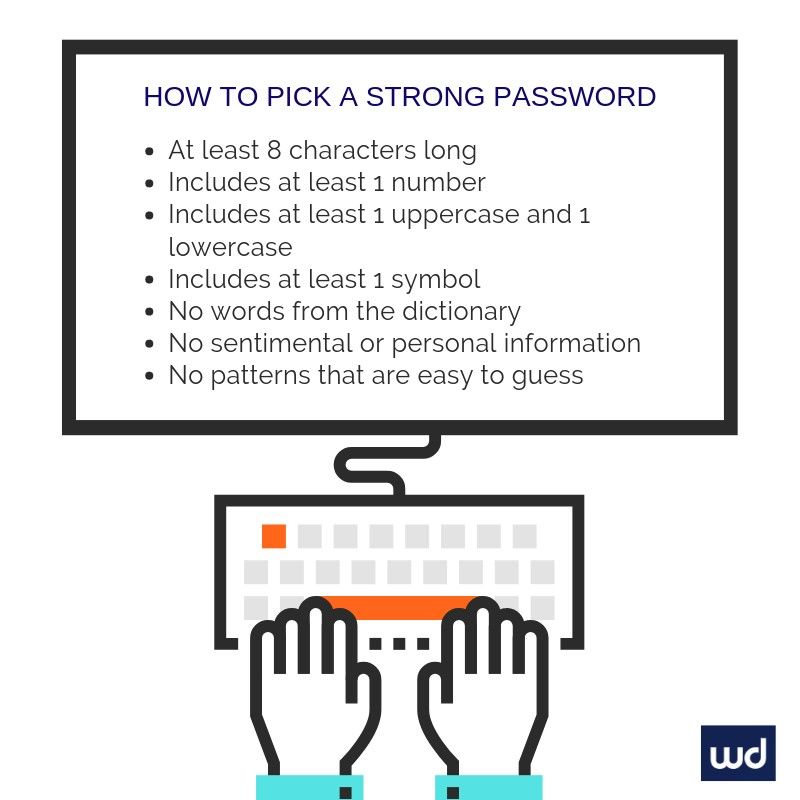
Change your passwords...then change them again: an oldie but a goodie – this one’s a timeless rule of thumb. Change your server and website admin passwords regularly, and utilise best password practices when generating new ones. As for your users, enforce strict rules around password creation to include a minimum of 8 characters, with an uppercase letter and a digit. Not sure what kind of password to choose? Use this handy tool or compare it against our list below.
Prevent user uploads: you’re asking for trouble by letting unknown users upload files onto your database. This is a huge security risk, even if they’re only looking to put up something minor. Although it might look innocent, it’s not always the case and can leave your website completely open to vulnerabilities. Exercise caution if you can’t avoid this.
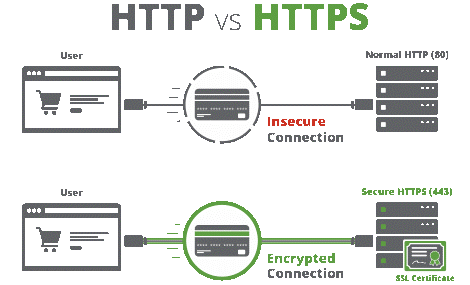
Use HTTPS: ah, this one’s a story for another day, but it’s also probably to be the most important step of all. Previously, all websites maintained a HTTP protocol in their URL, while portals like banks or password fields were protected with a secure certification known as HTTPS. These days, websites are shifting to assume a HTTPS URL, meaning they’re safe and secure for all visitors. In fact, Google automatically reverts to HTTPS itself for users inputting search queries, and while this is still a relatively new change, more than 31% of domains are now considered secure through the HTTPS protocol.
Keep plugins and software updated: it goes without saying that if your website CMS uses any specific software or plugins to operate, its a must that you keep them updated. Most plugin creators will roll out frequent versions so that you can avoid any potential threats.
Employ a secure host: no website can operate without a host, and you’re left trusting their servers to keep you secure. While they should be able to quickly restore your site if it’s hacked, they must be able to back up your data and provide technical support as needed. If you’re not sure how to get started with good website hosting, speak to a Website Design Australia expert.
Backup your data: just as we said before, backing up all the data on your website is be all and end all. Whether it’s your host’s responsibility or your own, regularly creating back ups will ensure you’re able to quickly restore or access your data if it is lost.
Audit your site frequently: whether you’re an expert in IT or not, having a professional assess your site frequently for potential vulnerabilities should be on top of your to-do list. They’ll be be able to spot any potential breaches and prevent them from occurring.
Get started
Above all, if you’re not sure where to start in getting your website safeguarded, it pays to employ a trusted professional. Get in touch with Website Design Australia’s team to put your website under lock and key.
